Ransomware continues to be a global threat, and cybercriminals using ransomware pose a significant risk to Australian organisations and households. The latest ACSC Annual Cyber Threat Report highlights there were nearly 500 ransomware related cybercrime reports received, an increase of 15 per cent from the previous financial year with ransom demands ranging from thousands to millions of dollars.
The report showed approximately one-quarter of reported cyber incidents impacted Australia’s critical infrastructure, including essential services such as health, education, communications, water, electricity and transport.
Cybercrime growing trend
As technology keeps evolving at a rapid pace, so do cybercriminals. Apart from newer forms of cyber threats, even the oldest tricks are not completely useless for these cybercriminals. They take these tricks out of their pocket and make modifications and updates to bypass security measures specially created for them. Specialisation is the current trend in cybercrime. One group might organise data breaches, another could specialise in malware or crypto-jacking, while a third could offer ransomware, phishing or mobile malware. Despite the differences in solutions, the point remains the same – the participants involved in these cyberattacks are professionals, armed with sophisticated tools of the trade, they are getting more aggressive every day, threatening businesses of all sizes.
A record of 86,2% of organisations suffers from a successful cyberattack last year according to the CyberEdge 2021 Cyberthreat Defence Report. Australia was found on the list of countries with the highest cyberattacks in 2019, with 81.6% of all surveyed companies being compromised at least once according to this report.


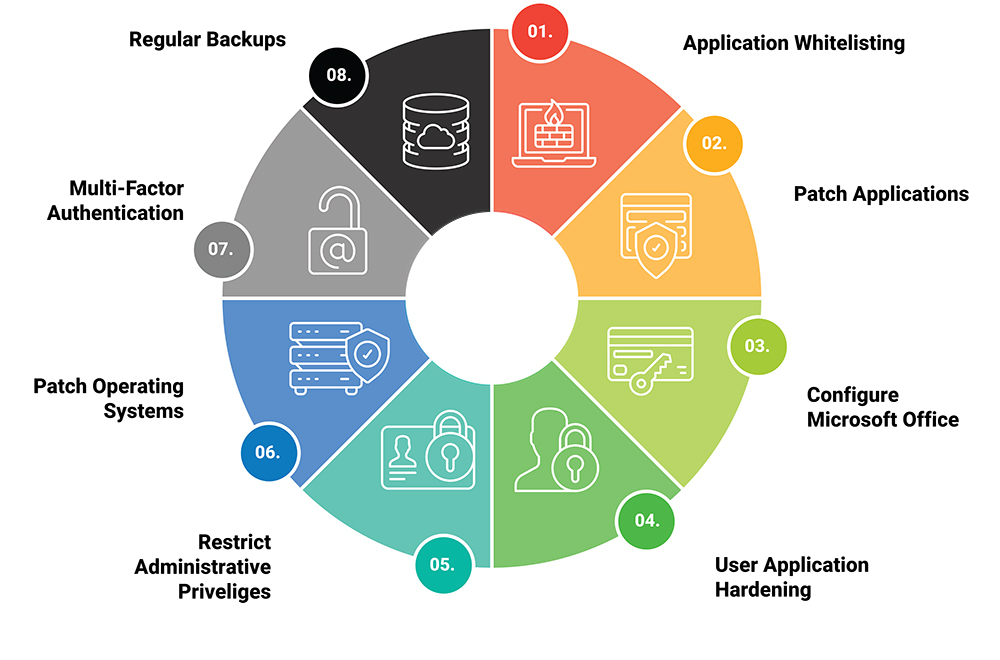
To assist organisations in protecting themselves against various cyber threats, the Australian Cyber Security Centre (ACSC) has developed a set of mitigation strategies prioritised by threat level. These strategies are known as Strategies to Mitigate Cyber Security Incidents. Of these mitigation strategies, the Essential Eight have proven to be the most effective.
What are the Essential Eight strategies?
1.Application Control or Application Whitelisting
This strategy strives to prevent ransomware, malware or any other execution of unapproved/malicious programs including .exe, DLL, scripts (e.g. Windows Script Host, PowerShell and HTA) and installers through unsecure applications. Basically, it prevents machines from running software libraries, scripts, installers, and other executable files.
2. Patch Applications
There may be security vulnerabilities in applications that allow malicious software to execute. This guideline explicitly refers to updates to third-party applications. By doing so, security patches and updates can be applied as quickly as possible. To implement this strategy, vulnerability scanners are essential for finding missing patches and updates, as well as eliminating solutions that no longer receive support from their vendors.
3. Configure Microsoft Office macro settings to block macros from the internet, and only allow vetted macros either in ‘trusted locations’ with limited write access or digitally signed with a trusted certificate. Within Microsoft Office applications, users have a certain amount of freedom when running macros. Users would typically be blocked from using macros by default unless they demonstrated a business need.
4. User Application Hardening
This strategy relates to the limitations that are placed on users’ applications. In web browsers, it is recommended that both ads and Java content from the internet should not be allowed to be processed and that Internet Explorer 11 should be disabled so that users cannot change these settings.
5. Restrict Administrative Privileges
This strategy is used to manage users with administrative privileges. During this process, trusted accounts are validated before access to systems and applications is granted, privileged accounts are blocked from using the internet, and privileged and nonprivileged users are assigned separate operating environments.
6. Patch Operating Systems
As part of this strategy, operating systems should be kept up to date. The main objective is to apply OS patches, updates, and security mitigations for internet-facing services within two weeks of their release – or within 48 hours if an exploit is found. The vulnerability scanner should detect any missing patches, and outdated operating systems should be replaced.
7. Multi-Factor Authentication
Using this strategy, all privileged accesses will need to be authenticated using multi-factor authentication. Multi-factor authentication can make it considerably more difficult for an adversary to steal legitimate credentials to facilitate further malicious activity on a network if implemented correctly.
8. Regular Backups
A backup is essential to ensure that information can be accessed following a cyber security incident (e.g., a ransomware attack). As part of this strategy, critical systems and information should be securely backed up and accessible. Organisations are encouraged to back up new and changed data, software, and configuration settings, under this strategy. Unprivileged accounts should be restricted to their own backup environments and all backup systems should be tested.
What are the Essential 8 parameters for measuring cybersecurity posture?
The different strategies that make up the Essential 8 are measured according to the level of cybercriminal tradecraft they aim to mitigate.
Any organisation’s cybersecurity posture is measured according to the level of cybercriminal activity they intend to mitigate. There are four different levels. Depending on an attacker’s overall capability, they may employ different levels of tradecraft for different operations against different targets.
Each strategy is ranked across four levels of maturity:
Maturity Level 0 – This maturity level signifies that there are weaknesses in an organisation’s overall cyber security posture.
Maturity Level 1 – This maturity level focuses on adversaries who are content to use commodity tradecraft that is widely available in order to gain access to, and likely control over, systems.
Maturity Level 2 – This maturity level addresses adversaries with modestly enhanced capability compared to the previous maturity level. Usually, adversaries spend more time on the effectiveness of their tools and on a target.
Maturity Level 3 – This maturity level is focused on adversaries who are more adaptive and less reliant on public tools and techniques. Adversaries take advantage of weaknesses in their targets’ cyber security postures, such as outdated software or inadequate logging and monitoring.
What is my organisation’s Essential Eight maturity level?
The Essential Eight should be integrated using a risk-based approach. As part of this effort, organisations should implement compensating security controls. This will ensure that the number of affected systems or users is as minimal as possible.
Different businesses have different compliance needs, so the most straightforward way to determine your compliance path is to ask for a professional Essential Eight maturity level assessment.
Organisations should strive for a level of maturity that is appropriate for their risk level. Normally, this means conducting a risk audit and a cybersecurity audit simultaneously.
It is also important to note that since the Essential Eight outlines a minimum set of preventative measures, organisations need to implement appropriate additional measures, if warranted by their environment, in addition to the ones within this maturity model.
To improve their cybersecurity posture and achieve the next maturity level, organisations need to know what risks they must address. They also need to know how much it will cost to do so, and what likely consequences they will suffer if they fail.
As cybersecurity consultatnts AWD can perform a compliance audit to determine your level of maturity in each strategy, and then help you create practices that ensure Essential Eight compliance. We can simplify the Essential Eight compliance journey and improve your cybersecurity posture assisting you the whole way. Take our easy Essential Eight Self-Assessment to determine your organisation’s Essential Eight Maturity level or contact us today and get your organisation Essential Eight ready.