
Onboarding a new IT solutions provider in Melbourne is a 10-step, governance-led process that confirms legal and procurement compliance, enforces Australian security and privacy requirements, plans and delivers technical integration, sets up SLAs and oversight, completes due diligence and pricing reviews, enables support and training, evaluates locality trade-offs, and builds in risk controls from the outset all coordinated end-to-end in AWD.
In Melbourne organisations, successful onboarding means aligning commercial, legal, security and technical workstreams in parallel, with clear approval gates and accountability. Businesses that treat onboarding as a structured, cross-functional program — not just a vendor handover reduce transition risk, realise value sooner, and stay compliant with Australian regulations such as the Privacy Act 1988, the Notifiable Data Breaches (NDB) scheme, and relevant Victorian legislation.

In practical terms, this involves agreeing on scope and KPIs before any access is granted, validating the provider’s controls and insurance cover, and developing a shared operational runbook for go-live and steady state.
AWD acts as the orchestration layer that makes this repeatable and auditable. It automates ABN/GST checks, generates compliant contracts and Data Processing Agreements, provisions environments and SSO using standardised blueprints, enforces SLA monitoring, and centralises risk, cost and governance reporting.
Step 1: Legal, Procurement and Compliance Checks (Melbourne-ready)
This step ensures the provider is legally registered, tax-compliant, and contracted under enforceable Australian law.
Verify supplier identity and tax status
- Confirm an active ABN via the Australian Business Register
- Check GST registration for correct 10% GST treatment
- Cross-check ASIC/ACN records, directors, and trading names
- AWD automates ABR/ASIC lookups and stores verification evidence
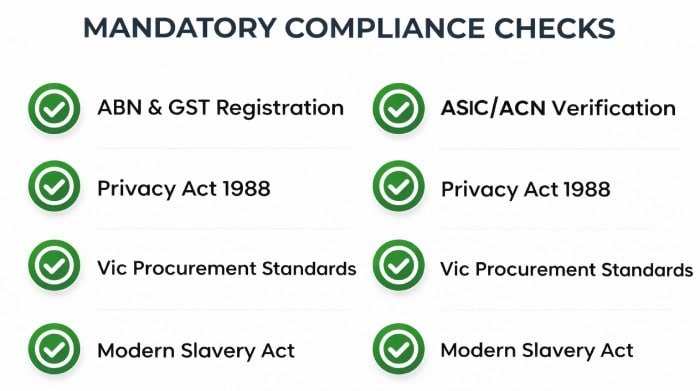
Align with Victorian procurement standards
- Public sector bodies align with Victorian Government Purchasing Board policies and approved panels
- Maintain probity through documented market scans and conflict-of-interest declarations
- AWD provides probity workflows and value-for-money scoring aligned to VGPB principles
Contracting under Australian law
Contracts should clearly cover:
- Victorian governing law and jurisdiction
- Unfair contract term protections under Australian Consumer Law
- IP ownership, liability, indemnities, privacy, subcontracting and termination rights
- Modern Slavery Act 2018 compliance
AWD’s AU/VIC clause library helps generate compliant contracts with tracked approvals.
Step 2: Security and Privacy Requirements (Australia-compliant)
This step ensures the provider meets national privacy and cybersecurity expectations.
Privacy and breach obligations
- Comply with the Privacy Act 1988 and Australian Privacy Principles
- Meet NDB reporting requirements “as soon as practicable”
- Victorian public sector agencies must also align with the Privacy and Data Protection Act 2014 and VPDSS
- Health data may also fall under the Health Records Act 2001
AWD’s DPA Builder maps APP obligations directly into contracts and tracks breach workflows.
Security controls and attestations

Common requirements include:
- Certification such as ISO/IEC 27001 or SOC 2
- Alignment with the ASD Essential Eight
- Encryption at rest and in transit
- MFA, least-privilege access, and privileged access controls
- Documented data residency (preferably Australia)
Step 3: Technical Integration and Environment Provisioning
Ensures the provider’s systems integrate securely and reliably.
Integration readiness
- API compatibility (REST, SOAP, gRPC)
- Versioning, schema standards, and error handling
- Sandbox testing and synthetic transactions
AWD’s Integration Catalogue assesses compatibility and deploys test environments quickly.
Identity, network and access
- SSO via SAML or OIDC (e.g. Entra ID, Okta)
- MFA and conditional access
- Secure VPN or private connectivity
AWD provides pre-built SSO connectors and role templates.
Environment setup
- Dev, test, UAT and production environments
- Infrastructure as Code for repeatable builds
- Logging, monitoring and alerting
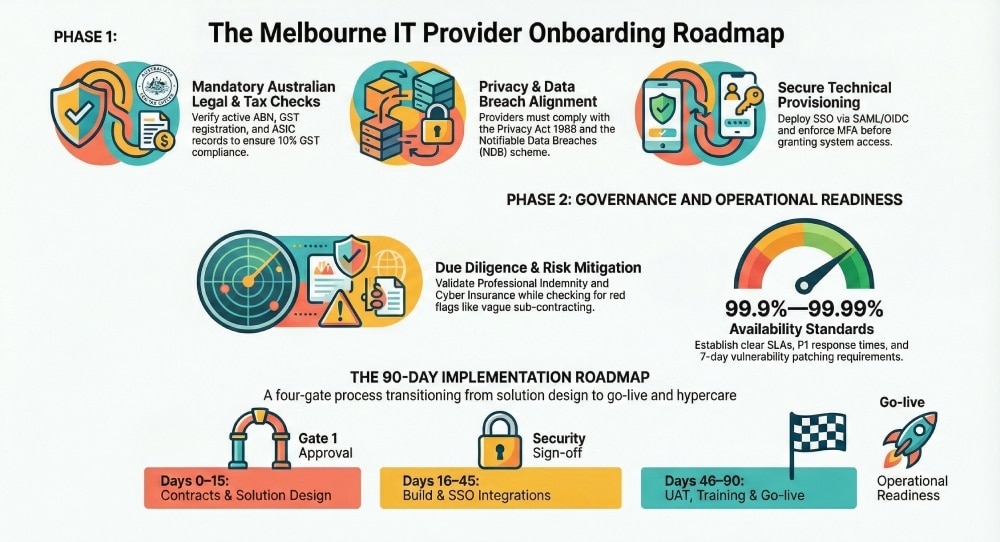
Step 4: Timeline, Governance and Change Control
A governance framework keeps onboarding on schedule.
Typical 90-day roadmap
| Phase | Focus | Gate |
| Days 0–15 | Contracts, due diligence, solution design | Gate 1 approval |
| Days 16–45 | Build, SSO, integrations | Security sign-off |
| Days 46–75 | UAT, training, documentation | Operational readiness |
| Days 76–90 | Pilot, hypercare, go-live | Go-live approval |
Governance structure
- Defined RACI model
- Fortnightly steering committee
- Change Advisory Board (CAB) processes
Step 5: SLAs, KPIs, Monitoring and Reporting

Performance expectations must be clearly defined and measurable.
Examples
- 99.9–99.99% availability
- 15-minute P1 response
- Critical vulnerabilities patched within 7 days
- Defined RTO/RPO targets
Step 6: Vendor Due Diligence and Red Flags
Before granting system access, confirm:
- Financial stability
- Adequate PI, Public Liability and Cyber Insurance
- Security certifications and pen test summaries
- Australian client references
Red flags include lapsed insurance, vague subcontractor arrangements, or resistance to sharing security evidence.

Step 7: Pricing, Billing and Total Cost of Ownership
Commercial clarity avoids future disputes.
- Confirm GST treatment and compliant invoices
- Model 3–5 year TCO including hidden costs
- Negotiate indexation caps and SLA credits
Step 8: Training, Documentation and Knowledge Transfer
Operational readiness depends on clear documentation and training.
- Runbooks and SOPs
- Architecture diagrams and configs
- Support and escalation pathways
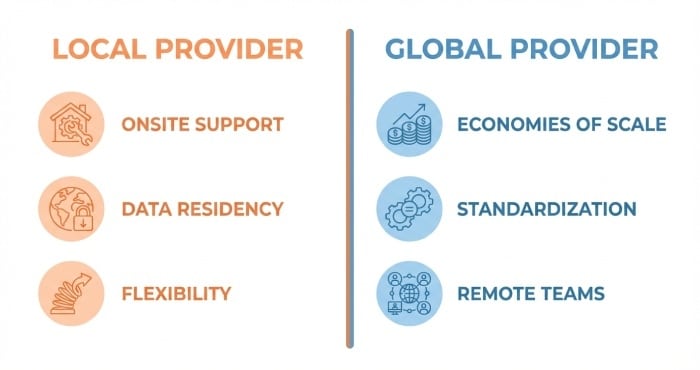
Step 9: Local vs Global Providers
Melbourne organisations often weigh:
| Factor | Local Provider | Global Provider |
| Onsite support | Faster | Limited |
| Data residency | Usually AU-based | May require APP 8 checks |
| Scale | Smaller | Larger |
| Cost | Flexible | Economies of scale |
Step 10: Common Onboarding Issues and Mitigation
Frequent problems include:
- Scope creep
- Delayed access approvals
- Integration mismatches
- Misaligned expectations
Conclusion
Onboarding an IT solutions provider in Melbourne is a structured, multi-disciplinary program, not just a procurement step. It requires compliance with Australian legal and privacy frameworks, strong security assurance, careful technical integration, and clear governance.By running onboarding through AWD, organisations turn a complex process into a repeatable, auditable and Melbourne-compliant workflow reducing risk, improving transparency, and achieving faster, safer go-lives.
