
Since 1995, phishing has been used by cyber criminals as an extremely lucrative way to obtain sensitive user information. In fact, according to the 2013 Microsoft Computing Safety Index, phishing costs users as much as $5 billion US dollars a year. The reason that phishing scams are so effective is because by and large, it relies on user vulnerabilities rather than technical vulnerabilities. Considering this, protecting your business from phishing attacks is a matter of user education rather than product deployment (although it is always advisable to have a strong anti-spam platform as part of a multifaceted security strategy). In this blog, we’ll be talking about how to spot a phishing email as well as a phishing website.

A Phishing Email
-
Comes from a suspicious sender address
If the sender’s address is similar, but not an exact match for official correspondence from the company it is supposed to be representing, then it’s most likely a scam. However, it’s important to remember that fraudsters are continually improving the appearance of their emails to make them look more official, so a legitimate looking email address is no longer a guarantee of authenticity.
-
Usually requests personal information
Such as a password, credit card number or bank details. A legitimate company would never request confidential information via email.
-
Often won’t refer to you by name
Because you’re one of thousands of other users the phishing email has been sent out to, it will probably contain a generic greeting such as ‘valued customer’ or ‘dear user’.
-
Provides a link or attachment to click on
Phishing emails often include links they want you to click on to capture your personal information or attachments that they need you to click on to begin installing malware on your system.
-
Demands urgent action
Fear mongering is a common phishing tactic with ominous phrases such as ‘your account has been compromised’ or ‘your account will be closed if you do not respond’. Legitimate companies will always call you if there is a serious problem with your account.
-
Often contains spelling and grammatical errors or is poorly formatted
Official communication from a large corporation is always professionally written and well edited before being sent out. Small spelling and grammar mistakes generally mean that the email hasn’t been put through this process and is probably not legitimate.
A Phishing Website
-
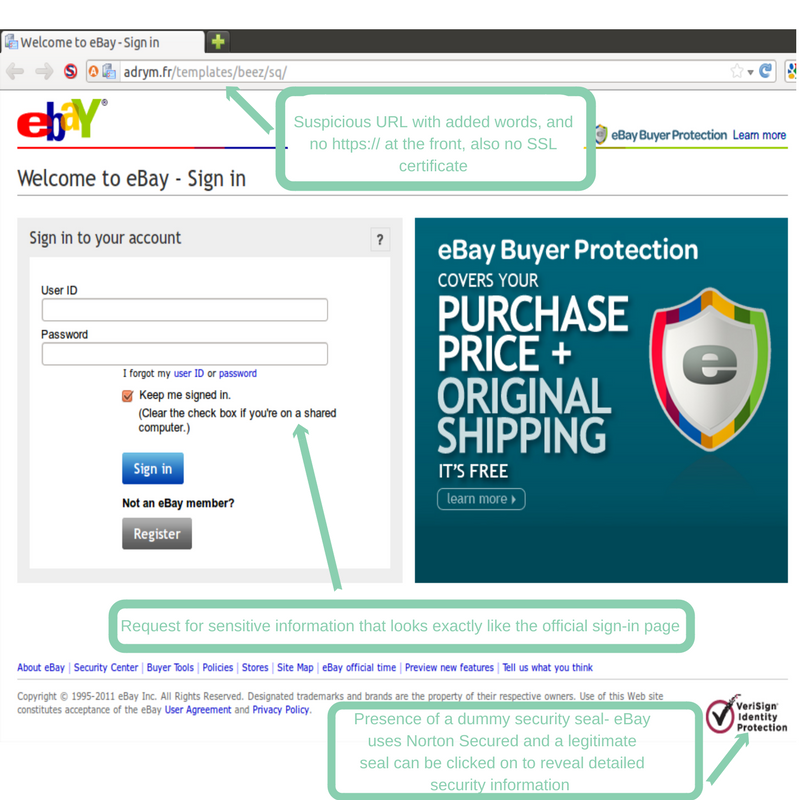
Can have a suspicious web address
Added words or domains, misspellings, the absence of an https:// at the beginning of the address or a forward slash at the end of the address and a long string of characters at the end of the URL are all red flags that the address may not be legitimate.
-
Pop ups
Often phishing sites use pop-ups as a means of garnering personal information. Be wary of pop-ups that immediately ask you to provide sensitive information.
-
Will accept fake passwords
If you are uncertain about the legitimacy of a site, sign in using a fake username and password- if it is accepted then you’re probably on a phishing site.
-
May or may not have certificate authority
The absence or presence of the little green lock in the upper left corner of the address bar used to be a reliable indication of whether a site is legitimate, but more advanced hackers have recently been able to construct phishing websites that have a legitimate SSL certificate.
URL testing
If you want to test the validity of a URL there are two key ways to do it. The easiest way is to simply hover over the link with your mouse, and the destination address will appear in the bottom left hand corner of your browser. If the URL is directing you somewhere other than where the link suggests, or looks at all suspicious, you can scan and check the rating of the site with a free scanning service like Norton SafeWeb or URLVoid.
If you are interested in learning more about implementing user education as part of a multifaceted network security strategy, please don’t hesitate to get in touch with us by calling 1300 855 651.
