
It seems like almost every day we hear about another company that has been the victim of a cyberattack. With Christmas around the corner, cybersecurity experts urge Australians to be extra vigilant about cybersecurity. Cybercriminals often use the busy festive season as an opportunity to exploit vulnerable people and businesses. To make sure you’re protected against cyberattacks, it’s important that cybersecurity measures like ISO 27001 and Essential Eight are implemented in your digital systems and practices. The Australian government also recommends seeking advice from cybersecurity consultants throughout the holiday season to ensure maximum cybersecurity protection. With safe cybersecurity protocols in place, Australians can feel at rest knowing their personal information is secured against any malicious activities or attacks.
Following on from our last article, we’re going to be covering more crucial cybersecurity strategies for protecting your business from a cyberattack.
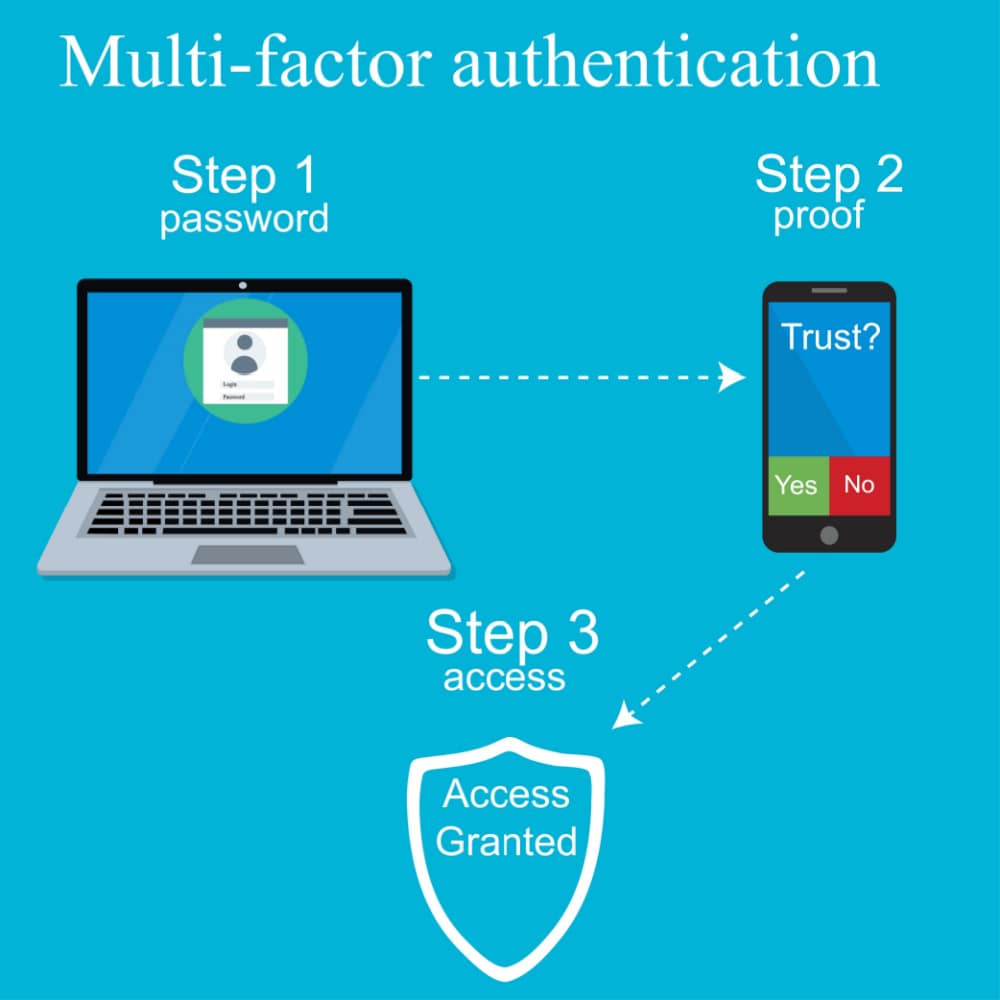
Multi-Factor Authentication
Multi-Factor Authentication (MFA) is becoming increasingly important in protecting users’ data and conforming to ISO 27001 security standards. Multi-factor authentication is an essential cybersecurity protocol to consider when securely accessing network profiles and online banking portals. ISO 27001 consultants recommend leveraging MFA across all sites, platforms, and networks, relying on it as an additional layer of authentication that can help keep your data secure even if passwords are stolen. Practicing robust cyber safety is not only wise from a personal standpoint, but ISO 27001 standards dictate that this level of security be maintained for businesses in order to comply with mandated regulations. Make sure you’re taking full advantage of MFA on your network, banking websites, and social media pages.
Computer Updates
Microsoft, Adobe, and Java products are vital to an organization’s security. By keeping these products current with the latest updates, you significantly reduce your computer systems’ vulnerability to cyber-attacks. Our service of automating “critical updates” helps companies further protect themselves from any threats that may arise and ensure their data remains secure.
Dark Web Research
Cyberattacks on businesses can be costly, both monetarily and in terms of reputation. Knowing what data is posted on the Dark Web before it’s used in a malicious attack can help organisations take action to protect their networks. By scanning the Dark Web in real-time and taking swift action, businesses can defend themselves from stolen credentials that have been posted for sale. This type of proactive approach offers crucial protection to organisations that are serious about defending against a data breach.
SIEM – Security Incident & Event Management
SIEM (Security Incident and Event Management) is a key method in protecting against advanced threats and ensuring compliance with regulations. It employs big data engines to analyse security and event logs from any connected devices, allowing quick detection of malicious activities, as well as alerting when compliance requirements are not met. By using powerful analytics tools to monitor the internal environment, organisations can gain the insight they need to proactively prevent possible attacks. Implementing SIEM-based log management offers the benefits of improved security, faster incident response times, and peace of mind that regulatory standards are being successfully maintained.
Web Gateway Security
As the internet continues to advance, new security threats arise on a daily basis. To protect organisations, web gateway security is paramount. Cloud-based security solutions detect emerging threats across web and email applications in real time. By doing so, hackers and malicious content can be blocked from reaching your network seconds after appearing online – enabling businesses to remain safe without disruption. Thus, it is important to incorporate an effective web gateway security system that can keep up with the ever-evolving speed of the digital era.
Mobile Device Security
It is imperative not to overlook mobile device security as it is becoming increasingly vulnerable to cybersecurity threats. Cybersecurity consultants suggest that investing in the right security solutions can help protect employee devices and networks from malicious hackers. Employers must take proactive measures and devise a strategy to secure corporate data on their mobile devices, ensuring the integrity of personal and organisational information. Doing so helps minimise attempts by criminals looking to gain access to your network through employees’ phones or tablets. Having a mobile security plan in place is essential to keeping you, your employees, and your customers safe online.

Firewall
A firewall is a key component of cybersecurity, providing a critical layer of protection against malicious activity. However, to ensure optimal cybersecurity defences, you can also turn on Intrusion Detection and Intrusion Prevention features for an extra level of security. By sending a log file to a managed SIEM, your cybersecurity team can get the most out of your firewall by applying analytics and finding patterns in order to identify potential threats quickly and eliminate them from your networks. If the technical side of cybersecurity is daunting for your IT team, get in touch with some cybersecurity consultants – they will be able to provide advice on how best to use all the available tools.
Encryption
Ensuring email security is a huge priority in modern-day communication, as email remains one of the primary forms of business exchange. Companies must protect sensitive email traffic when it is being sent, stored, and viewed; that is why encryption is so important. Whenever possible, files should be encrypted both at rest and in motion, especially on mobile devices. Rmail makes this easy with its comprehensive email encryption features; allowing users to encrypt and decrypt email content quickly and efficiently without sacrificing performance or usability. Protecting data through encryption can be the difference between a secure email environment and a compromised one.

Backup
It’s essential to have disaster recovery plans in place, and backups play a large part in ensuring one’s data is safe, secure, and up-to-date. There are many integral steps one should take to eliminate the possibility of data loss or corruption; backing up locally, to the cloud, and having an “office” backup for every month of the year is highly recommended. To ensure that your disaster recovery plan is effective, testing your backups must be done often; if any uncertainty remains as to whether or not your backups are working correctly, don’t wait – contact us right away.
These are some key points to bear in mind during the Christmas period, but of course, each business is different and has unique cybersecurity risks. If you want specific advice tailored to your company’s needs, AWD’s cybersecurity consultants and IT experts can help. We offer a free initial consultation so please do not hesitate to get in touch. Keep your business safe this holiday season – Book your free consultation!
