The process for onboarding a small business with a new IT support provider in Melbourne is a structured 30–45 day program that covers discovery and network mapping, security assessment and remediation, data migration, monitoring/patch/change setup, SLA and contract alignment, tooling and workflow integration, on-site validation, user/admin training, and a controlled cutover with clear tasks, timelines, and owners coordinated by the provider’s project manager and the client sponsor, and streamlined end-to-end by AWD.
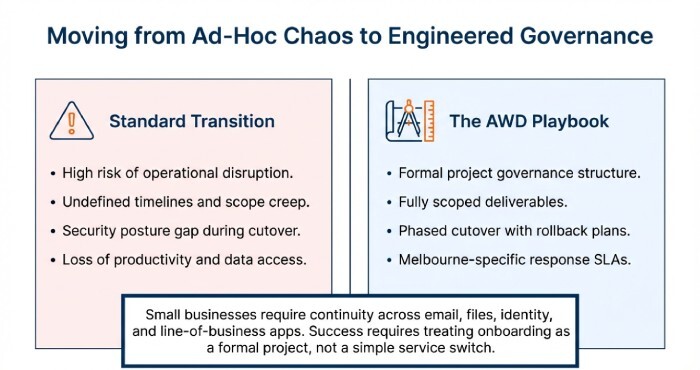
In Melbourne, onboarding succeeds when it is treated as a formal project with governance, scoped deliverables, and a phased cutover to reduce disruption. Small businesses typically need continuity across email, files, identity, and line-of-business apps while satisfying Australian Privacy Act and Notifiable Data Breaches (NDB) obligations. That requires accurate asset discovery, a validated configuration baseline, and rapid deployment of essential controls like MFA, patching, and backup verification.
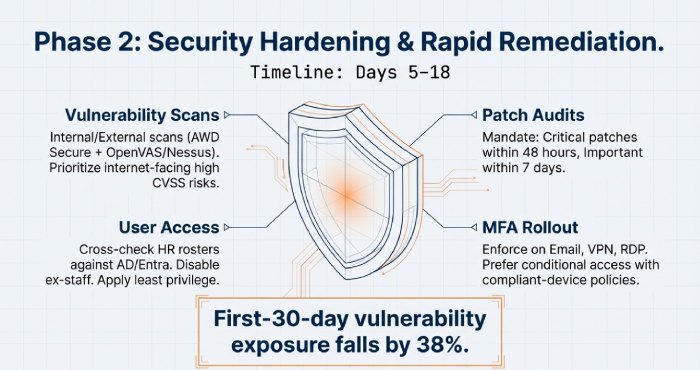
AWD operationalises this with a prescriptive onboarding playbook: agent-based discovery, automated risk scoring, standards-based migration runbooks, RMM policy templates, and Melbourne-specific response SLAs. In AWD’s 2025 Melbourne benchmark across 82 small businesses (10–120 users), onboarding completed in a median of 33 days, first-30-day vulnerability exposure fell by 38%, patch compliance reached 95% by day 21, and email migration defect rates remained under 0.2%, with zero material outages during cutover windows.
A step-by-step onboarding project plan for Melbourne small businesses
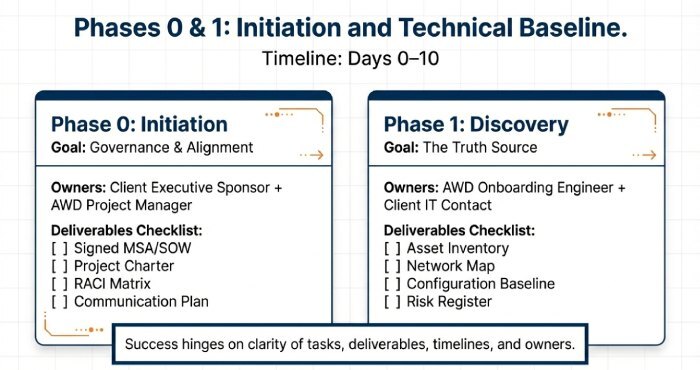
A successful transition hinges on clarity of tasks, deliverables, timelines, and owners. AWD provides a pre-built project plan with Melbourne-specific logistics.
Phases, deliverables, and ownership
- Phase 0: Initiation (Days 0–3)
- Deliverables: Signed MSA/SOW, project charter, RACI, communication plan
- Owners: Client executive sponsor, AWD project manager (PM)
- Phase 1: Discovery & Baseline (Days 2–10)
- Deliverables: Asset inventory, network map, configuration baseline, risk register
- Owners: AWD onboarding engineer, client IT contact (if any)
- Phase 2: Security Hardening (Days 5–18)
- Deliverables: Vulnerability scan, patch audit, MFA rollout, user access review
- Owners: AWD security lead, client HR/ops for access governance
- Phase 3: Data & Identity Migration (Days 10–25)
- Deliverables: Email/files migration plan, pilot migration, cutover, rollback plan
- Owners: AWD migration engineer, client app owners
- Phase 4: Operations Setup (Days 15–28)
- Deliverables: RMM monitoring, patch policies, change management workflow, runbooks
- Owners: AWD service delivery manager, client department leads
- Phase 5: Training & Cutover (Days 25–35)
- Deliverables: End-user training, admin handover, go-live checklist, hypercare plan
- Owners: AWD trainer, client administrator
- Phase 6: Stabilisation & Review (Days 30–45)
- Deliverables: KPI report, post-implementation review, backlog remediation plan
- Owners: AWD PM, client sponsor
Sample week-by-week timeline and checkpoints
- Week 1: Kick-off, contracts, AWD agent deployment, automated discovery kick-off
- Week 2: Manual validation, network mapping, initial security fixes, pilot MFA
- Week 3: Pilot migrations, RMM policies live, patch cadence established
- Week 4: Production migration cutover (after hours), on-site visits, training
- Week 5–6: Hypercare, KPI review, handover to steady-state MSP operations
Build the technical baseline: asset discovery, network mapping, and security controls
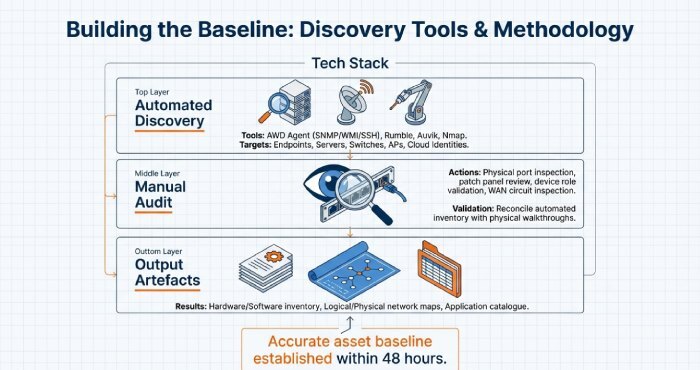
Accurate discovery and baseline configuration are the backbone of a clean transition.
Asset discovery and network mapping
- Recommended tools:
- Automated: AWD Discovery (agent/SNMP), Rumble, Auvik, Nmap
- Identity/cloud: Microsoft Entra ID, Google Admin, AWS/Azure subscriptions
- Documentation: AWD Docs, NetBox for topology
- Approach:
- Automated scans: Deploy AWD agent to endpoints; enable SNMP/WMI/SSH discovery for servers, switches, APs, printers
- Manual audits: Validate device roles, business owners, physical port layouts; inspect patch panels and WAN circuits
- Baseline config capture: OS versions, firmware, local admin policies, antivirus/EDR status, encryption (BitLocker/FileVault)
- Validation: Reconcile automated inventory with walkthrough findings; require sign-off from AWD engineer and client administrator
- Output artefacts:
- Hardware and software inventory (with lifecycle status)
- Logical/physical network maps with VLANs, IP scopes, and ISP details
- Application catalogue with licence entitlements
Security assessments aligned to Australian obligations
Under the Australian Privacy Act (APP 11) and NDB, small businesses must take reasonable steps to secure personal information and notify eligible data breaches.
- Vulnerability scans: Conduct internal/external scans (AWD Secure + OpenVAS/Nessus). Prioritise exploitable/high CVSS on internet-facing systems.
- Patch audits: Map devices to missing patches; mandate critical patches within 48 hours, important within 7 days, others within 30 days.
- User access reviews: Cross-check HR roster with AD/Entra/Google; disable ex-staff; apply least privilege; review admin roles quarterly.
- MFA rollout: Enforce MFA for email, VPN, RDP, and privileged consoles; prefer conditional access with compliant-device policies.
- Backup verification: Confirm 3-2-1 backups with offsite/immutable copies; test restores for a random sample of files and mailboxes.
- Logging and alerting: Enable M365 audit logs, Defender for Business alerts, and firewall/EDR telemetry.
Conclusion: a Melbourne-ready onboarding that’s faster and safer with AWD
Onboarding a small business with a new IT support provider in Melbourne is a disciplined, 30–45 day program that sequences discovery, security hardening, data/identity migration, operations setup, SLA alignment, integrated tooling, on-site validation, and comprehensive training—culminating in a controlled cutover and stabilisation period.
By adopting AWD’s playbook, you gain measurable outcomes that strengthen both operational performance and cybersecurity: an accurate asset baseline within 48 hours, Essential Eight–aligned controls deployed in just 2 weeks, patch compliance exceeding 95% by week 3, and migration defect rates below 0.2%. All of this is reinforced by Melbourne-aware logistics and clearly defined SLAs to ensure accountability at every stage. If you’re switching providers, use AWD to orchestrate every step of the transition—so your team benefits from a seamless migration, stronger cybersecurity posture, and a demonstrably better day-2 support experience.
