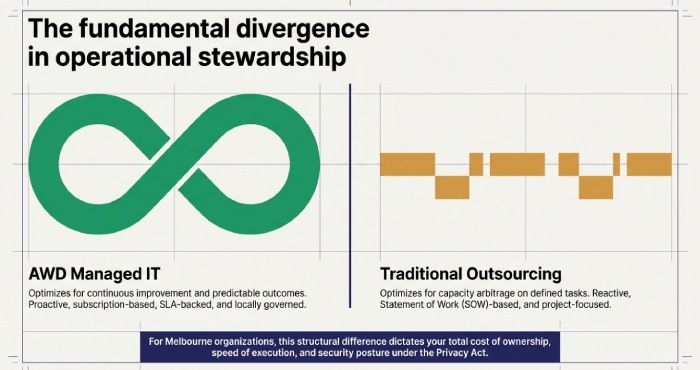
Managed IT solutions in Melbourne provide proactive, subscription-based, SLA-backed, locally governed end-to-end stewardship with Australian data residency, while traditional IT outsourcing is typically reactive, SOW- or time-and-materials-based, project/task-focused, often leveraging offshore teams with looser operational SLAs and variable compliance controls.
Managed IT and traditional IT outsourcing both transfer operational load from your in-house team, but they are optimised for different outcomes: managed IT aims for continuous improvement and predictable outcomes across your environment, while traditional outsourcing aims for capacity arbitrage on defined tasks or projects. For Melbourne organisations navigating Australian Privacy Principles (APPs), Victorian public sector data rules and Essential Eight uplift, this difference materially affects risk, speed and total cost of ownership.
Methodologically, this guide compares the two models as they are delivered in Melbourne today, drawing on AWD’s field benchmarks (illustrative, based on recent engagements) and local market norms across contract design, onboarding, service-level agreement (SLA) , delivery footprint, security,governance and sector-specific needs. Each section concludes with how AWD implements the capability so you can map features to outcomes in context.
Contracts, Pricing and Onboarding in Melbourne
Contract structures and pricing models
Managed IT solutions
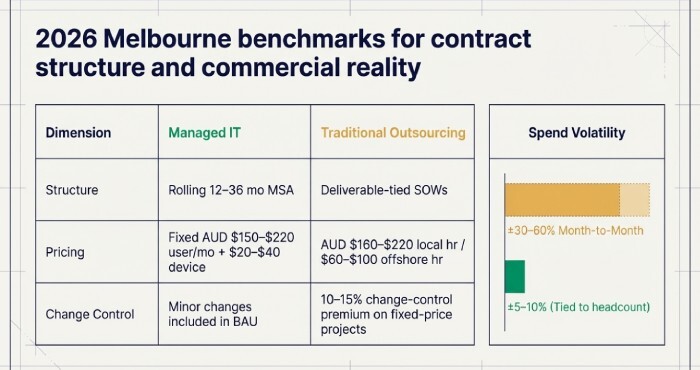
- Contract: master services agreement (MSA) + service catalogue; rolling 12–36 months.
- Pricing: predictable, usually per-user or per-device subscription; fixed monthly fee with clear inclusions.
- Billing: monthly in arrears; usage adjustments are transparent (add/remove users).
- Change control: minor changes included; major projects scoped separately but at pre-agreed rates.
Traditional outsourcing
- Contract: statement(s) of work (SOW) tied to deliverables; extensions by change requests.
- Pricing: time-and-materials (T&M) or fixed-price per project; rate cards by role and location.
- Billing: milestone or hourly; variability month-to-month is common.
- Change control: reinvigorates scoping; change premiums are standard.
Melbourne cost benchmarks (illustrative, 2026)
- Managed IT: AUD $150–$220 per user/month for core services; devices +$20–$40 each.
- Traditional outsourcing: AUD $160–$220 per local engineer hour; AUD $60–$100 offshore; fixed-price projects add 10–15% change-control overhead.
- Volatility: outsourcing spend varies ±30–60% month-to-month; managed IT typically ±5–10% due to headcount changes.
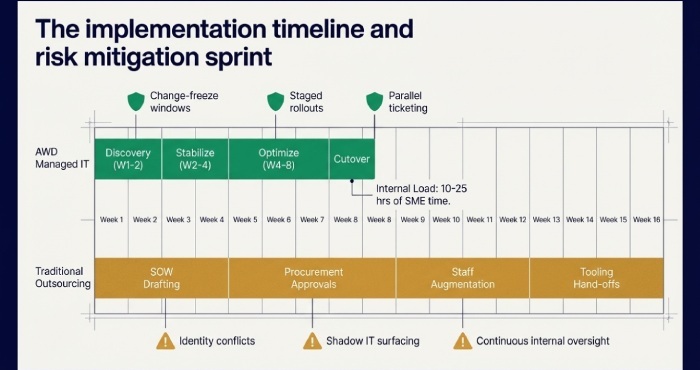
Implementation and onboarding: steps, timelines and risks
Managed IT onboarding (typical 4–8 weeks)
- Discovery and baselining (Week 1–2): asset and identity inventory, security posture (Essential Eight), backup health, network maps.
- Stabilise (Week 2–4): deploy agents (RMM/EDR), patch baselines, backup tests, MFA hardening, ticketing integration, knowledge capture.
- Optimise (Week 4–8): SOP runbooks, automations, monthly governance cadence, roadmap for 90-day and 12-month improvements.
- Cutover: go-live with joint support; change-freeze window and rollback plans.
Traditional outsourcing engagement (typical 8–16 weeks to steady state)
- Requirements and SOW drafting; approvals and procurement.
- Knowledge transfer sessions; staff augmentation onboarding.
- Tooling hand-offs; Key performance indicators (KPIs) set per project.
- Execution with periodic status updates.
Internal resource need: managed IT requires concentrated SME time for discovery (10–25 hours across roles); outsourcing requires continuous internal oversight for scope compliance and change management.
Migration risks
- Data exposure during tooling switch (ticketing, RMM).
- Identity conflicts (duplicate accounts, weak MFA).
- Shadow IT surfacing without owners.
Mitigation: staged rollouts, change freeze windows, parallel ticketing, and tested rollback playbooks reduce risk.
SLAs, Operations and Delivery Footprint
SLAs, response times and escalation procedures
Managed IT
- SLAs: proactive monitoring; 24×7 critical alerting; tiered response (e.g., P1 within 15–30 min, P2 within 1 hr, P3 same business day).
- Escalation: clearly documented L1→L3 and vendor pathways; service credits for misses.
- Performance monitoring: continuous (RMM, SIEM); monthly SLA scorecards with MTTR, FCR, patch compliance and backup success.
Traditional outsourcing
- SLAs: often tied to project milestones or ticket queues without proactive commitments.
- Escalation: relies on project managers; technical escalations can be ad hoc.
- Monitoring: usually your tools; provider reacts upon notification rather than instrumenting.
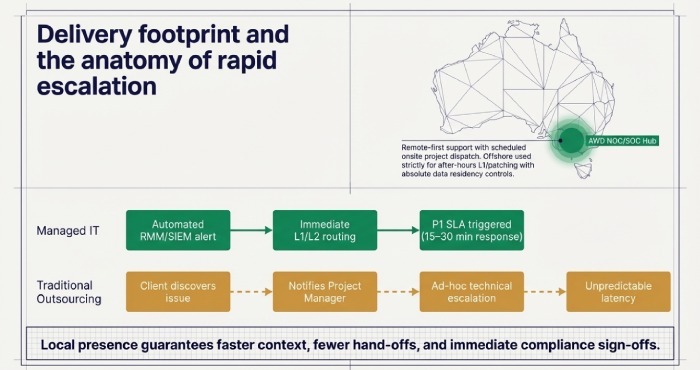
Local presence, remote support and offshore use
Managed IT
- Delivery: local NOC/SOC with remote-first support; scheduled onsite for projects and complex incidents.
- Offshore: used selectively (after-hours L1, patch windows), with data residency controls.
- Practical impact: faster context, fewer hand-offs, better stakeholder management; simpler compliance sign-offs.
Traditional outsourcing
- Delivery: blends offshore delivery and local project management; cost-efficient but may increase latency and cultural/context gaps.
- Practical impact: increased coordination overhead; potential data transfer outside Australia.
Monitoring and performance visibility
- Managed IT: includes integrated monitoring (endpoint, server, cloud), security analytics and user experience metrics; reports are operationalised into roadmaps.
- Outsourcing: monitoring is often your responsibility; providers respond rather than detect.
Security, Data Sovereignty and Compliance
Obligations relevant to Melbourne organisations
- Australian Privacy Principles (APPs) under the Privacy Act 1988 (Cth): collection, use, disclosure, storage and cross-border disclosure requirements.
- Victorian public sector and OVIC guidance (if applicable): stronger data handling and protective data security standards.
- Data sovereignty: Australian residency for customer, ticket and log data is often a contractual requirement.
- Essential Eight maturity: the de facto benchmark for cyber resilience uplift across sectors.
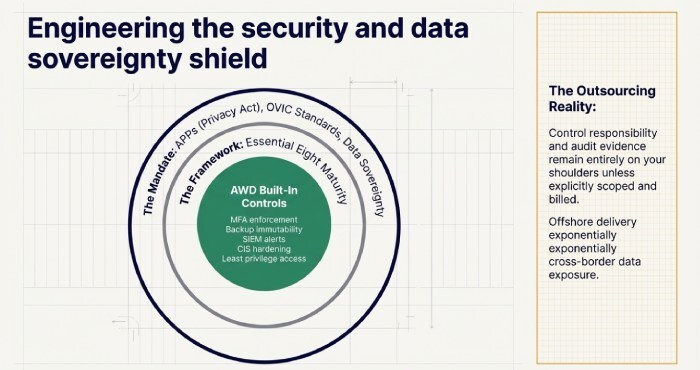
Managed IT vs traditional outsourcing on compliance
Managed IT
- Built-in controls: MFA enforcement, least privilege, CIS/Essential Eight hardening, backup immutability, SIEM alerts.
- Evidence: periodic compliance reporting, control maps and audit support.
- Cross-border: contractual guardrails on offshore access and data export.
Traditional outsourcing
- Control responsibility: remains with the client unless explicitly scoped.
- Evidence: ad hoc; audits require extra work and fees.
- Cross-border: offshore delivery increases exposure unless specifically constrained.
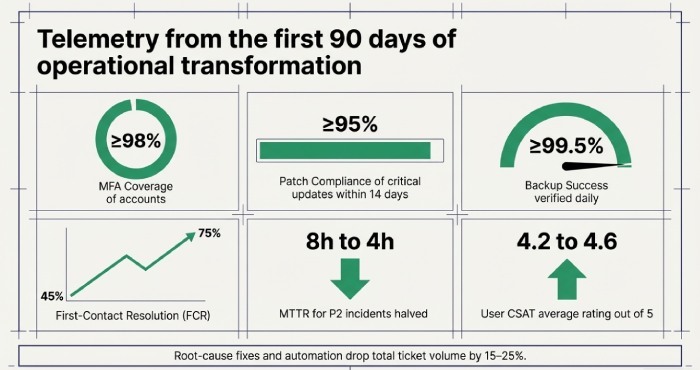
Security benchmarks (illustrative, first 90 days after AWD onboarding)
- MFA coverage: raise to ≥98% of accounts.
- Patch compliance: ≥95% of critical updates within 14 days.
- Backup success: ≥99.5% daily success with quarterly restore tests.
- Endpoint EDR coverage: ≥98% of enrolled devices.
- Phishing click rate: reduce by 40–60% with awareness and simulations.
Selection Best Practices, Governance and KPIs
Vendor evaluation criteria for Melbourne organisations
- Technical fit: toolchain compatibility (M365, Azure/AWS, RMM/EDR), Essential Eight roadmap, industry-specific needs (e.g., CPS for health).
- Commercial fit: clear inclusions/exclusions, rate cards, exit rights, service credits.
- Delivery model: local presence, after-hours coverage, offshore posture, Australian data residency.
- Security posture: documented control mapping, incident response runbooks, breach notification terms.
- Cultural fit: communication cadence, stakeholder management and change management maturity.
- Proof-of-concept (POC): 30-day pilot for a subset of users/sites, including reporting and a mock incident.
- References: Melbourne clients of similar size/sector; request sample scorecards and governance packs.
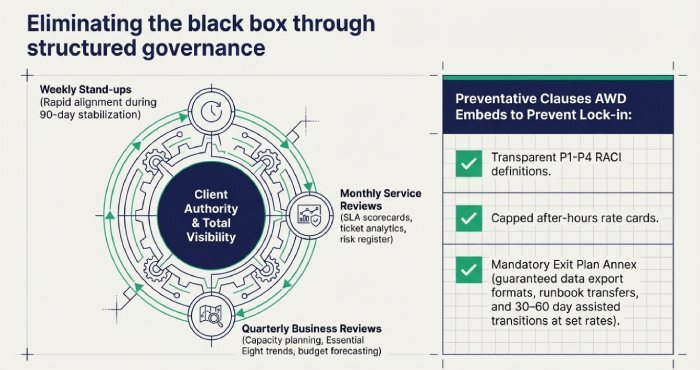
Governance practices and reporting dashboards
Expected practices with managed IT
- Monthly service reviews: SLA adherence, ticket analytics (FCR, reopen rate), risk register, roadmap progress.
- Quarterly business reviews (QBRs): capacity planning, budget vs forecast, project pipeline, security posture trends.
- Dashboards: MTTR, MTTD, patch compliance, backup success, identity risk, CSAT, asset compliance, change success rate.
Traditional outsourcing governance focuses on
- Project status reports, burn rates, milestone tracking and acceptance testing.
Recurring problems and contract clauses to prevent them
Common issues
- Communication breakdowns: unclear severity definitions; lack of single owner.
- Hidden costs: out-of-scope items, after-hours fees, on-site surcharges.
- Vendor lock-in: proprietary tooling, opaque data, punitive exits.
Preventive clauses and practices
- RACI and definitions for P1–P4; named service owner; weekly stand-ups during first 90 days.
- Transparent service catalogue; capped after-hours rates; onsite bundles; clear “reasonable use.”
- Exit plan annex: data export formats, runbook transfer, 30–60 day assisted transition at set rates.
- Benchmarking and termination for convenience with fair notice.
Use Cases, Integration Challenges and Mitigation
Sector-specific pros and cons in Melbourne
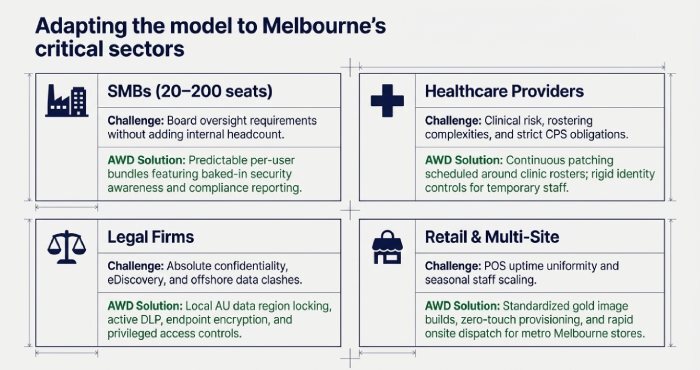
SMBs (20–200 seats)
- Managed IT: high value via predictable spend and security uplift; minimal internal IT required.
- Outsourcing: cost-effective for one-off projects but can create operational gaps.
- AWD: offers per-user bundles including security awareness and compliance reporting to satisfy board oversight without adding headcount.
Healthcare providers
- Managed IT: continuous patching, identity control and audit evidence reduce clinical risk; supports after-hours with strong access controls.
- Outsourcing: project-strong but may underdeliver on day-to-day security hygiene unless tightly managed.
- AWD: can map controls to CPS/privacy obligations and schedule maintenance around clinic rosters to minimise disruption.
Legal firms
- Managed IT: local presence, data sovereignty and rapid incident response are critical; DLP (data loss prevention) and eDiscovery support matter.
- Outsourcing: offshore components may clash with client confidentiality clauses.
- AWD: keeps ticket and log data in AU regions and implements device encryption, DLP and privileged access controls aligned to legal confidentiality.
Retail and multi-site
- Managed IT: standardised endpoint builds, POS uptime SLAs and scalable onboarding for seasonal staff.
- Outsourcing: suitable for store-fit projects; weaker for uniform day-to-day support across sites.
- AWD: delivers gold images, zero-touch provisioning and onsite dispatch windows for metro Melbourne stores.
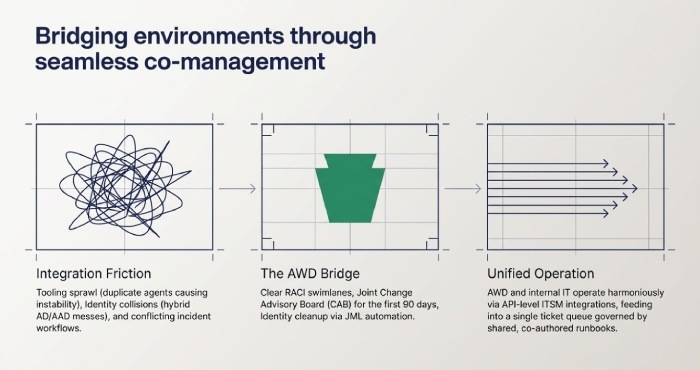
Integration with in-house IT and legacy systems
Common interoperability issues
- Tooling sprawl: duplicate agents (RMM, AV) cause instability.
- Identity collisions: hybrid AD/AAD misconfigurations; stale privileges.
- Legacy apps: vendor-locked appliances; unsupported OS versions.
- Process drift: conflicting change and incident workflows.
Mitigation strategies
- RACI matrix with clear swimlanes (who runs what).
- Tooling rationalisation plan with change-freeze windows and rollback tests.
- Identity clean-up (JML automation, least privilege reviews, break-glass accounts).
- Co-author runbooks; integrate ITSM tools via application programming interface(APIs) for a single queue of work.
- Joint CAB for high-risk changes during the first 90 days.
Operational outcomes: illustrative AWD field data (composite)
- First-contact resolution (FCR): improves from 45–55% to 65–75% within 60 days.
- MTTR for P2 incidents: reduced from ~8 hours to ~4 hours by month three.
- Ticket volume per user: drops 15–25% as root-cause fixes and automations mature over 90 days.
- User CSAT: increases from ~4.2/5 to ~4.6/5 with clear comms and faster resolution.
FAQs
How do I avoid paying twice once for managed IT and again for projects?
Define “business-as-usual” (BAU) inclusions in the service catalogue and set a dollar/hour threshold that triggers project scoping. AWD uses pre-agreed rate cards and will bundle small improvements into BAU during the 90-day stabilisation window to prevent nickel-and-diming.
Can a managed IT provider work with my existing MSP or project outsourcer?
Yes, with a RACI, joint CAB for changes, and API-level integrations between ITSM tools to strengthen cybersecurity coordination. AWD routinely co-manages environments, operating through a single ticket queue and shared runbooks to prevent hand-off friction.
What if my board insists on Australian-only delivery?
Select a provider that offers Australian data residency and onshore delivery guarantees in contract. AWD can commit to AU-only personnel and platforms for sensitive sectors, with named resources and compliance reporting.
Do I lose control over my environment with managed IT?
You should gain control via standardisation and transparent reporting. AWD provides admin access policies, break-glass procedures and monthly governance so you retain visibility and authority while offloading execution.
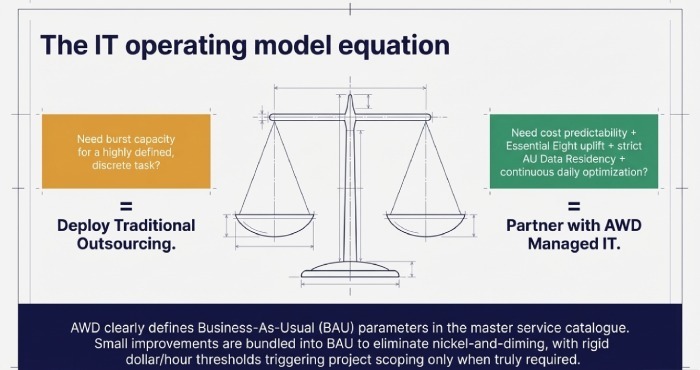
Conclusion: Choosing the right model for Melbourne and how AWD helps
In Melbourne, the decisive differences come down to operating model and accountability: managed IT delivers proactive, subscription business model, SLA-backed outcomes with local governance and compliance evidence, while traditional outsourcing is best for scoped tasks and projects priced by the hour or milestone with variable operational guarantees. If you need predictable costs, security uplift aligned to APPs and Essential Eight, and continuous improvement, managed IT is usually the better fit; if you need burst capacity for a defined project, traditional outsourcing may be ideal.
AWD ties these principles to execution: a Melbourne-centric managed IT service with transparent per-user pricing, 4–8 week onboarding, Australian data residency, measurable SLAs and governance that links daily operations to your risk register and roadmap. Whether you adopt AWD as your primary managed IT partner or in a co-managed model alongside an outsourcer, the emphasis is the same predictable value, auditable compliance and tangible improvements your executives and auditors can see month after month.
To validate fit, consider a 30-day AWD pilot: deploy to a representative user group, instrument the environment, run a mock incident and compare the resulting KPIs, SLA adherence and security posture uplift against your current baseline. That evidence will make the managed IT vs outsourcing decision clear, in Melbourne terms that matter cost predictability, compliance and day-to-day performance.
