
For Australian businesses operating in Melbourne, dependable managed IT services are essential to keeping day-to-day operations running smoothly, supporting business continuity, and enabling growth. A strong managed service provider (MSP) delivers 24/7 support, proactive monitoring, and results-driven IT support to safeguard revenue and maintain network stability. Whether you’re an IT Manager modernising your IT infrastructure or an executive leading digital transformation, the right Melbourne-based partner can streamline technology solutions, minimise risk, and fast-track business growth without compromising compliance or data security.
What to compare in Melbourne’s MSP market
Industry requirements and local conditions
- Sector alignment: Ensure the MSP understands your regulatory and operational environment (e.g., healthcare, manufacturing, finance) and can align cybersecurity controls and disaster recovery with your risk profile. Ask for tailored IT consulting and a clearly defined IT strategy.
- Tools and technology stack: Choose providers with certified technicians, documented regular maintenance schedules, and transparent system update processes to prevent configuration drift.
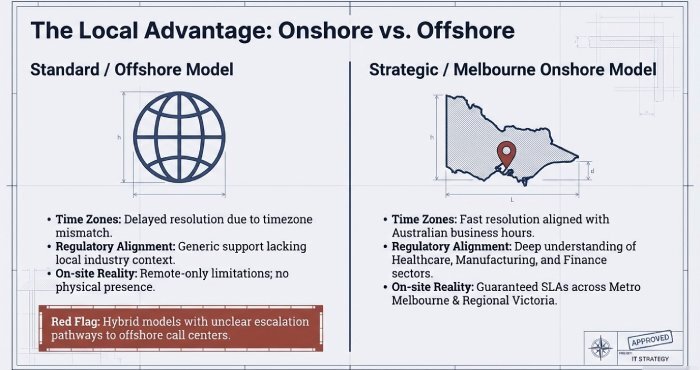
Onshore versus offshore service desk
- Onshore, Australian-based teams often provide faster resolution of urgent issues and a stronger understanding of Melbourne time zones and local compliance requirements.
- If an MSP operates an offshore or hybrid model, confirm the escalation pathways, 24/7 service desk coverage, and how round-the-clock support is resourced within the SOC and NOC.
On-site support and remote assistance
- Confirm guaranteed on-site support SLAs across metropolitan Melbourne and regional Victoria not just remote support commitments.
- For cost-effective service delivery, look for proactive monitoring that reduces unnecessary site visits, supported by clearly documented service desk playbooks.
Local client references and industry credibility indicators
- Request local references from Australian businesses in industries similar to yours. Look for Melbourne-based case studies (for example, logistics, manufacturing, or food production organisations such as Eversons Food Processors).
- You’ll often see acronyms in tenders MSP, MITS, PMS so ask providers to clearly define their scope of services. Also, review their vendor ecosystem and partnerships with organisations such as IBM, Dell, Lenovo, and major cloud computing providers.
Cyber security: Safeguards and Compliance
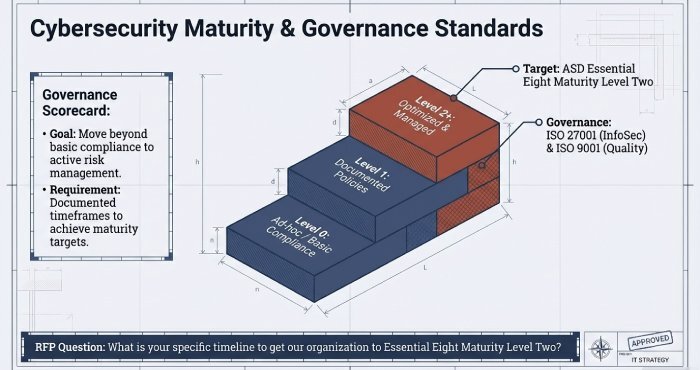
ASD Essential Eight maturity levels and standards compliance
- Request documented ASD Essential Eight maturity targets, including clear timeframes to achieve Maturity Level Two or higher.
- Confirm the MSP’s governance frameworks (for example, ISO 27001 for information security and ISO 9001 for quality management). These certifications help ensure consistent IT support, effective incident management, and ongoing continuous improvement.
MDR/SOC and EDR/XDR
- A mature MSP should provide managed detection and response (MDR) delivered through a 24/7 Security Operations Centre (SOC), integrating EDR/XDR across endpoints, servers, and cloud workloads.
- Ensure proactive monitoring detects lateral movement, privilege escalation, and unusual identity activity within Microsoft 365 and Microsoft Azure.
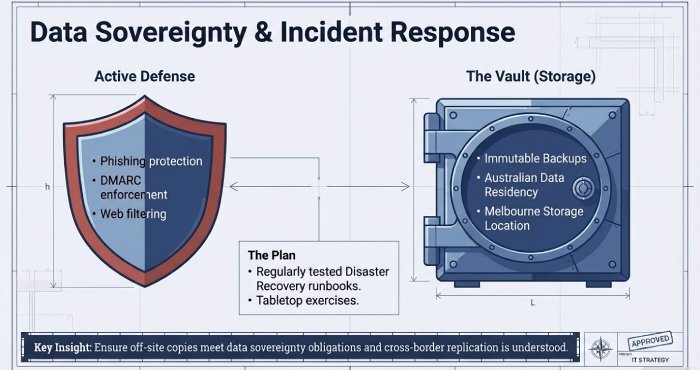
Email and web filtering, and data security
- Assess phishing protection, DMARC enforcement, and web filtering aligned to your organisation’s risk appetite.
- Data security should include data loss prevention (DLP), encryption at rest and in transit, and robust identity management practices.
Back-up, disaster recovery, and incident response
- Insist on immutable back-ups, regularly tested disaster recovery runbooks, and RPO/RTO targets aligned with your business continuity requirements. Confirm that off-site copies are stored in Australia or in Melbourne where required to meet data sovereignty obligations.
- Verify that incident response retainers are in place, along with regular tabletop exercises and support for cyber insurance readiness, including policy alignment, evidence preparation for underwriters, and clearly defined breach notification procedures.
Cloud and infrastructure: Azure-first versus multi-cloud
Strategy: Azure-first, multi-cloud or hybrid network environments
- An Azure-first approach suits organisations running predominantly Microsoft-based environments, while a multi-cloud strategy can help diversify risk and optimise workloads. A capable managed service provider should clearly explain the trade-offs, pricing models, and network architecture considerations.
- Hybrid network environments should incorporate SD-WAN, Zero Trust access principles, and identity-based policies to maintain network stability and strengthen security.
Migrations, performance, and cost optimisation
- For system migrations, request a phased implementation plan, defined rollback procedures, and appropriate workload right-sizing. Look for automation in system updates and consistent patch management baselines.
- Ongoing optimisation should include resource tagging, right-sizing, reservation planning, and monitoring of data egress to remain cost-effective without compromising performance.
Data sovereignty in Australia and Melbourne
- Clarify where your data and back-ups are stored. Many Melbourne organisations require Australian data residency to meet compliance obligations, so confirm the hosting regions and whether any cross-border replication is used by cloud service providers.
Microsoft 365: licensing and security hardening
Licence optimisation and governance
- Ensure licence optimisation across Microsoft 365 SKUs to avoid unnecessary costs. Look for software recommendations aligned to user roles, along with governance controls for Microsoft Teams and Microsoft SharePoint, including lifecycle management, retention policies, and external sharing restrictions.
Identity management, Conditional Access, and tenant security
- Expect baseline security hardening across Microsoft 365, including multi-factor authentication (MFA) for all users, Conditional Access policies, privileged identity management, and continuous monitoring of security posture through Secure Score assessments.
- Security controls should align with recognised frameworks such as ISO/IEC 27001 and the Australian Signals Directorate’s Essential Eight maturity model to support audit readiness and regulatory compliance.
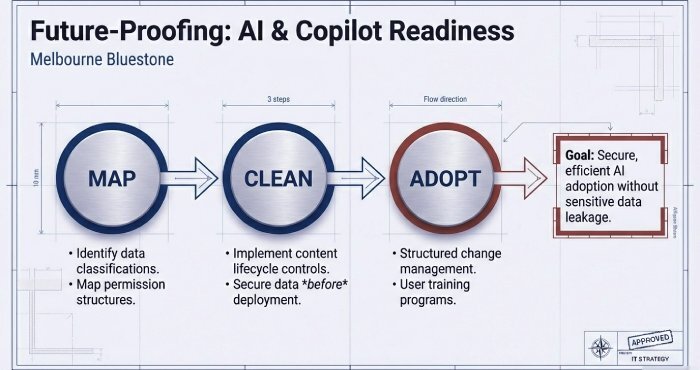
Readiness for AI tools and user adoption
- A mature managed service provider should help prepare your environment for Microsoft Copilot by mapping data classifications, content lifecycle controls, and permission structures.
- Support user adoption through structured change management, targeted training programs, and service desk guidance that reinforces secure and efficient working practices.
Service delivery and support coverage
24/7 support, proactive monitoring, and escalation
- Confirm the combination of 24/7 support, round-the-clock help desk availability, and proactive monitoring across endpoints, servers, and cloud environments to help prevent outages and protect business continuity.
- Ensure clear escalation pathways to certified technicians, with well-defined service tiers for urgent incident resolution.
On-site support and field services in Melbourne
- Confirm the availability of on-site support within agreed service windows across Melbourne’s CBD and surrounding suburbs, including access to spare parts and efficient hardware procurement processes to support rapid system restoration.
- Ask how the managed service provider coordinates vendor and warranty management with original equipment manufacturers such as IBM, Dell, and Lenovo to help speed up the replacement of faulty hardware under warranty.
Pricing, SLAs, and selection checklist
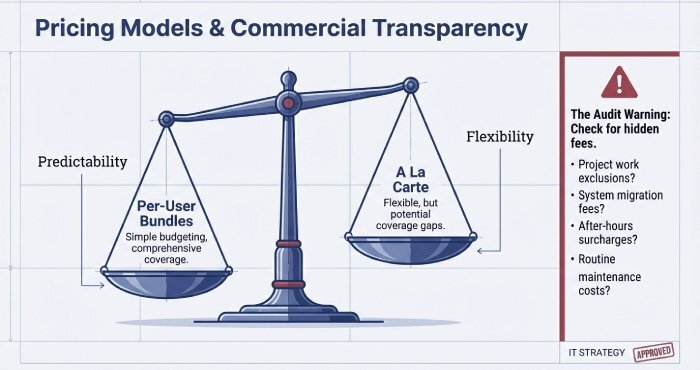
Pricing models: per-user bundles versus a la carte
- Per-user bundled pricing simplifies budgeting for managed IT and support services, while a la carte pricing can offer flexibility but may introduce service gaps. Look for scalable solutions and contracts that can adapt as your headcount changes.
- Make sure you clearly understand what is included and excluded, such as project work, system migration, after-hours on-site assistance, or break-fix support.
Response SLAs, on-site SLAs, and reporting
- Insist on response, restoration, and on-site service SLAs that align with your organisation’s risk profile and business continuity requirements.
- Reporting and KPI metrics should include ticket volumes, mean time to resolution (MTTR), patch compliance, back-up success rates, cyber maturity targets such as the Australian Signals Directorate’s Essential Eight posture, and disaster recovery test outcomes.
RFP questions to ask
- Which Australian-based staff members support your SOC, NOC, and help desk services?
- What are your Essential Eight maturity targets and implementation timeline?
- How do you ensure Australian data residency, particularly for Melbourne-based operations?
- Can you provide at least three Melbourne client references, including measurable outcomes such as uptime, cost savings, and recovery performance?
- Which controls under ISO/IEC 27001 and ISO 9001 are applied to our environment?
Red flags to watch for
- Vague managed detection and response (MDR) or SOC capabilities, or the absence of a clear EDR/XDR implementation.
- No documented incident response plans or disaster recovery testing schedules.
- Service delivery relying entirely on offshore support with unclear 24/7 coverage.
- Hidden fees for routine maintenance, patching, or system updates.
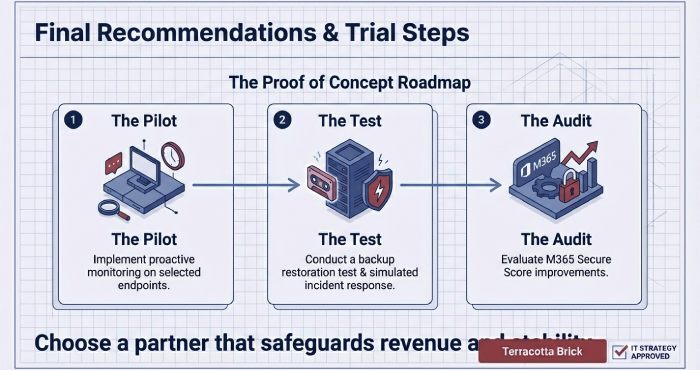
Trial and proof-of-concept testing
- Pilot proactive monitoring across a selected group of endpoints.
- Conduct a back-up restoration test and a simulated incident response exercise.
- Trial security hardening for Microsoft 365 and evaluate improvements in Secure Score performance.
Partners, certifications, and local credibility signals in Australia
Ecosystem and credibility
- Look for established partnerships with cloud technology providers and original equipment manufacturers, such as Truis, supported by recognised vendors including IBM, Dell, and Lenovo.
- Local client references are particularly important. Confirm proven outcomes for Australian businesses across multiple industries, with a focus on Melbourne-based case studies demonstrating reliability, security performance, and operational improvement.
Procurement language and service expectations
- In Australian tenders, you may encounter acronyms such as MSP, MITS, and PMS request clear definitions of service scope and delivery boundaries.
- Ensure service levels are aligned with your IT strategy, operational rhythm, and compliance obligations, with technology solutions supporting business continuity, cyber resilience, and disaster recovery planning.
