Selecting a partner for managed IT solutions in Melbourne is a strategic decision that shapes how your business technology performs every day. The ideal IT company blends managed IT services with proactive IT support, robust cybersecurity controls, and reliable network monitoring to reduce downtime and elevate business productivity.
Look for an IT solutions provider that understands your IT network, offers flexible support options, and can align technology solutions with your business models and compliance requirements. Businesses across various industries rely on managed IT solutions Melbourne to streamline their technology infrastructure, enhance cybersecurity, and ensure reliable day-to-day operations.
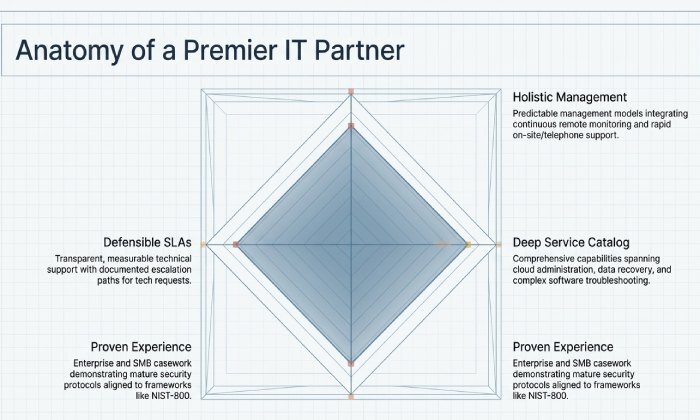
What a strong provider looks like
- Holistic technology management: Continuous remote monitoring, rapid on-site support, and responsive telephone support built into a predictable management model.
- Deep service catalog: From cloud services and computer repair to data recovery, software installation, and software troubleshooting, all guided by seasoned IT technicians.
- Proven industry experience: An IT firm that can reference enterprise IT and SMB casework, demonstrate security management maturity, and implement security protocols aligned to frameworks like NIST-800.
- Clear SLAs and response times: Measurable help desk support and technical support with
documented escalation for tech support requests and troubleshooting.
Vendor ecosystem and tools that matter
Evaluate the provider’s partnerships and tooling. For example, many top-performing teams deploy Microsoft 365, VEEAM for backup and data recovery, Sonic Wall and Cisco for network security, and 3CX for unified communications and telephone support. These platforms enable secure IT solutions and faster response times across your IT applications and cloud environments.
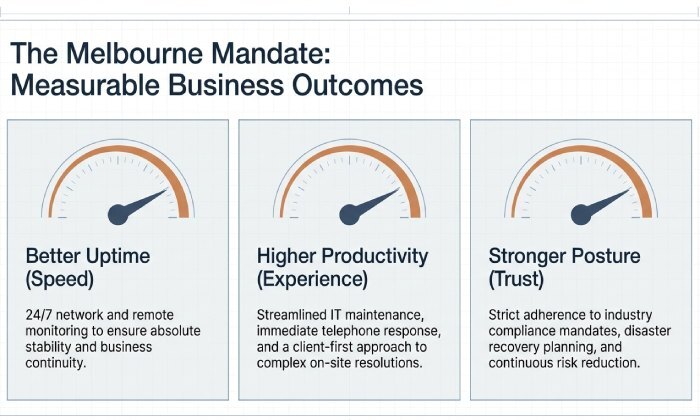
Why Managed IT Solutions Matter for Melbourne Businesses
Melbourne organisations compete on experience, speed, and trust. Managed IT solutions provide the foundation: a stable IT network, proactive IT support to prevent incidents, and cybersecurity that safeguards every technology asset. With the right managed IT services model, you gain peace of mind through predictable management, risk reduction, and business continuity planning that includes disaster recovery and robust data recovery.
Business outcomes you can measure
- Better uptime through 24/7 network monitoring and remote monitoring.
- Higher business productivity with streamlined IT maintenance and a client-first approach to IT support.
- Faster resolution via on-site support for complex issues and immediate telephone support for quick wins.
- Stronger compliance posture across industry compliance mandates, supported by mature security management and ongoing technology assessment.
Understanding Managed IT: Core Services and Delivery Models
Managed IT services span daily operations, security, and strategy. A comprehensive service provider integrates these layers into cohesive technology solutions tailored to business IT needs.
Core services you should expect
- IT support and help desk support: Multi-channel technical support via telephone support, a self-serve portal for tech support requests, and scheduled on-site support when needed.
- Network operations: Real-time network monitoring, remote monitoring, and IT network optimisation with network setup and continuous IT maintenance.
- Endpoint and user services: Computer repair, software installation, and software troubleshooting handled by certified IT technicians.
- Cloud services and backups: Managed cloud environments, cloud services administration, data recovery through immutable backups, and disaster recovery runbooks aligned to business continuity.
- Security management: Patch orchestration, identity access controls, and security protocols that reinforce cybersecurity and compliance.
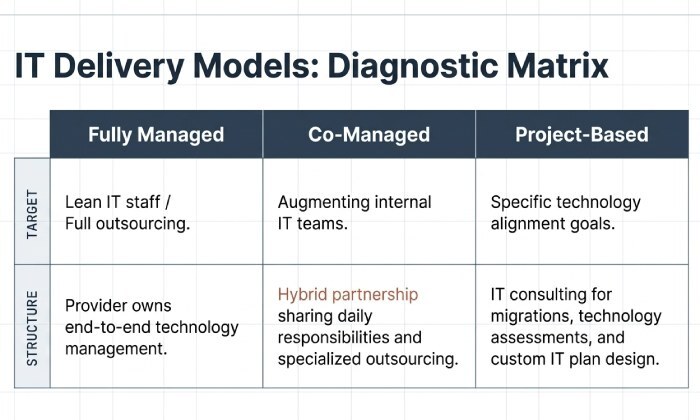
Delivery models to consider
- Fully managed: The IT company owns end-to-end technology management, ideal for lean IT staff or fully outsourced IT services.
- Co-managed: Hybrid IT services that augment your IT team, blending outsourcing IT with an IT partnership model that shares responsibilities.
- Project-based: IT consulting for migrations, technology assessment, and custom IT plan design to align with technology trends and technology alignment goals.
Pricing transparency and fit
Look for pricing tiers and payment plans that match your custom IT plan. The best service provider will align support options with budget and growth projections while keeping information technology purchasing simple and defensible.
The Melbourne Advantage: Local Expertise, Compliance, and Proximity
A Melbourne-based IT partner brings local market knowledge, faster on-site support, and sharper awareness of regional compliance requirements. Proximity improves response times, accelerates network troubleshooting, and strengthens communication with your IT clients and stakeholders.
Local context with a global lens
While Melbourne needs local presence, your IT company should also track nationwide IT managed services best practices. For example, providers such as EssentialNet Solutions (ENS) at ensusa.com, ProSource at getprosource.com, and ITonDemand at itondemand.com publish guidance relevant to operations across Melbourne.
Assessing Your Business Needs: Audit, Risk, and Budget Alignment
Before you shortlist providers, run a structured technology assessment to clarify business IT needs, risks, and costs.
A practical assessment framework
- Inventory and classify: Map every technology asset, IT applications, and IT network segment; document business-critical dependencies.
- Identify IT challenges: Capture recurring incidents, troubleshooting gaps, and technology challenges that impede business productivity.
- Evaluate controls and compliance: Review security protocols, audit trails, and compliance requirements in your sector.
- Build the IT plan: Translate findings into a custom IT plan with service scope, response times, and milestones. Decide where outsourcing IT or co-managed models fit best.
- Budget and governance: Tie support options, payment plans, and pricing tiers to predictable management and risk reduction targets.
Strategic alignment
Use IT consultation to align technology solutions with growth goals and technology trends. Your IT partnership should include measurable outcomes for business continuity, disaster recovery, and cybersecurity hardening.
Security First: Cybersecurity, ACSC Essential Eight, and Compliance Obligations
Security is non-negotiable. Your provider’s approach to cybersecurity should integrate security management, compliance by design, and continuous network monitoring.
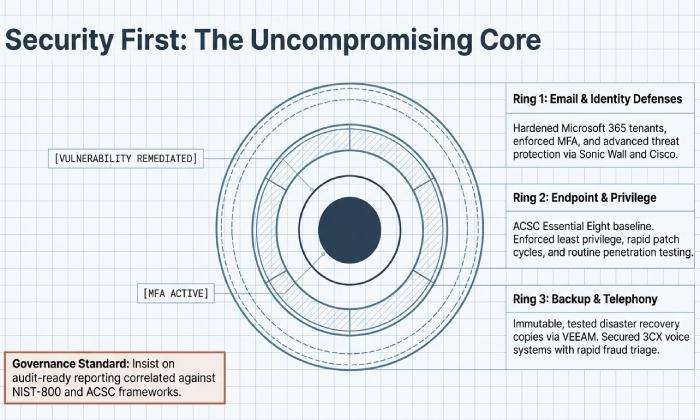
Implementing the ACSC Essential Eight
For Melbourne organisations, the ACSC Essential Eight offers a practical baseline. Your managed IT services partner should demonstrate how each control is implemented and validated through remote monitoring and on-site support where required.
How strong providers operationalise security
- Patch and privilege: Enforce least privilege and rapid patch cycles across servers, endpoints, and cloud services to protect the IT network.
- Backup and recovery: Test data recovery and disaster recovery frequently; maintain offline or immutable copies with platforms such as VEEAM.
- Email and identity defenses: Harden Microsoft 365 tenants, apply MFA, and deploy advanced threat protection backed by Sonic Wall and Cisco controls.
- Telephony security: Protect 3CX or other voice systems; ensure telephone support teams can triage suspected fraud and social-engineering attempts quickly.
- Policy and training: Maintain security protocols, run awareness campaigns, and monitor compliance continuously.
Minimum controls checklist
- Documented incident response with clear telephone support escalation
- 24/7 remote monitoring and alerting integrated with proactive IT support
- Regular penetration testing and vulnerability remediation
- Tested data recovery objectives mapped to business continuity
- Evidence of compliance against ACSC Essential Eight and references to NIST-800 where appropriate
Governance, audits, and reporting
Demand audit-ready reporting that proves compliance and supports industry compliance reviews. A trusted IT provider will correlate logs from information technology systems, demonstrate risk reduction over time, and provide responsive service during audits. They should also guide you through technology purchasing for secure IT solutions and validate the fit of cloud environments with compliance obligations whether you operate solely in Melbourne or maintain ties to Melbourne FL markets.
Why this matters for selection
When evaluating managed IT solutions, prioritise providers that embed cybersecurity across technology management and day-to-day IT support. Insist on clear ownership of security management tasks, transparent SLAs for telephone support and on-site support, and documented processes for computer repair, IT maintenance, and software troubleshooting. Ultimately, the right IT company will function as a true technology partner, aligning managed IT services and technology solutions to your risk appetite, compliance needs, and growth strategy.
Cloud and Modern Workplace: Microsoft 365, Azure, AWS, and Hybrid Options
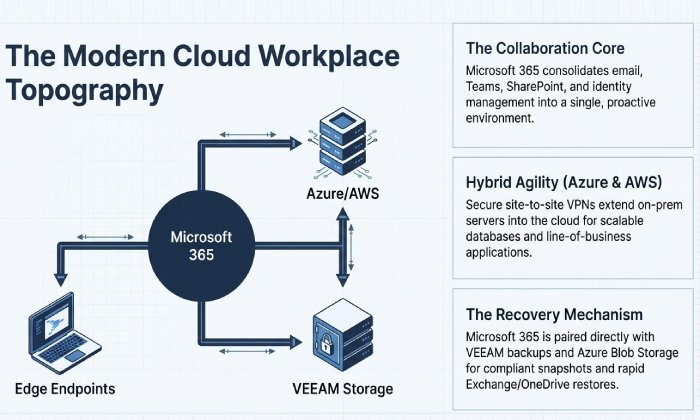
Microsoft 365 as the collaboration core
Modern cloud services have become the backbone of managed IT solutions, especially for distributed teams in Melbourne. Microsoft 365 consolidates email, Teams, SharePoint, and security management into a cohesive suite that elevates business technology and simplifies technology management. With managed IT services orchestrating identity, endpoint hardening, and telephone support integration through 3CX, Melbourne IT clients gain proactive IT support and predictable management across their IT network and IT applications. An experienced IT company will layer cybersecurity controls that align with NIST-800, implement security protocols like MFA and conditional access, and deliver on-site support for change management or user training.
Microsoft 365 is also a launchpad for data recovery strategies. Paired with VEEAM backups and Azure Blob Storage, it enables compliant snapshots, rapid restore of Exchange or OneDrive, and disaster recovery for critical mailboxes vital for business continuity and risk reduction. When issues arise, help desk support and technical support teams can triage tech support requests quickly, minimising downtime and improving business productivity.
Azure, AWS, and hybrid IT services
Azure and AWS are ideal cloud environments for scalable databases, line-of-business apps, and enterprise IT workloads. A trusted IT provider will architect hybrid IT services that extend your on‑prem servers into the cloud, using secure site‑to‑site VPNs on Sonic Wall or Cisco firewalls, and network monitoring with remote monitoring agents to ensure performance and uptime. These technology solutions deliver the agility of cloud services without abandoning existing technology assets, keeping compliance requirements intact for industry compliance frameworks.
Hybrid designs are particularly effective for organisations with latency‑sensitive IT challenges, regulated data, or branch offices from Orlando to Jacksonville, Miami, and Oviedo. With the right IT plan and IT consultation, your IT partner can stage migrations, validate software installation, and handle software troubleshooting while maintaining telephone support and on-site support during cutovers in Melbourne.
Governance, security protocols, and compliance in the cloud
Whether in Azure or AWS, enforce least privilege, encryption at rest and in transit, and standardised security management aligned to NIST-800. Routine technology assessment, continuous remote monitoring, and network monitoring of virtual networks and gateways keep cybersecurity posture strong. Define retention for data recovery, build disaster recovery runbooks, and test restores quarterly to meet compliance and business IT needs while ensuring peace of mind.
Network, Endpoint, and Infrastructure Management Best Practices
From core to edge: visibility and control
Robust network monitoring across switches, wireless, and firewalls provides early warning and proactive IT support for congestion, failures, or threats. Remote monitoring platforms surface anomalies, while on-site support handles physical remediation and network setup when cables, optics, or power systems fail. Managed IT services standardise configurations, enforce security protocols, and integrate telephone support escalation for incidents that impact voice or video across the IT network.
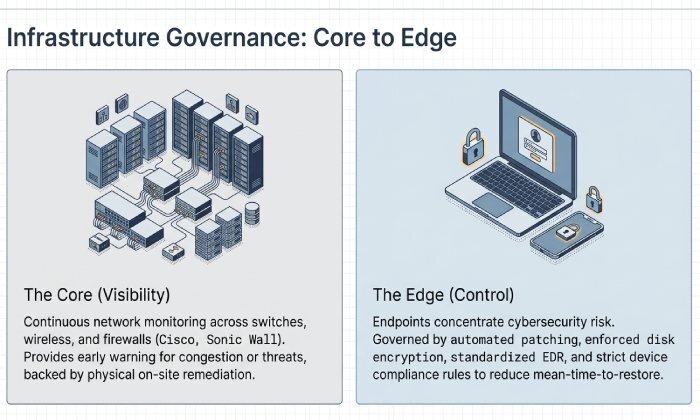
Endpoint hardening, IT maintenance, and computer repair
Endpoints are where cybersecurity risk concentrates. Managed IT solutions should automate patching, enforce disk encryption, and standardise antivirus, EDR, and device compliance rules. Routine IT maintenance, timely computer repair, and swift troubleshooting reduce mean time to restore and protect business technology. IT technicians document software installation baselines, approve updates for critical IT applications, and record software troubleshooting steps for consistent technical support.
Technology management for risk reduction
Proactive technology management ties infrastructure health to measurable outcomes availability, response times, and business productivity. Aligning these with compliance commitments and security management objectives ensures risk reduction without sacrificing user experience.
Service Level Agreements (SLAs), Response Times, and Support Coverage
What to expect in an effective SLA
An SLA defines response times for critical, high, and normal incidents; outlines support options; and clarifies coverage windows for remote monitoring, telephone support, and on-site support. Look for proactive IT support commitments such as patch cadence, network monitoring thresholds, and quarterly technology assessment reviews so managed IT services don’t become purely reactive. Mature SLAs include explicit data recovery objectives (RPO/RTO), compliance reporting, and escalation paths to senior IT technicians and architects within the IT firm.
