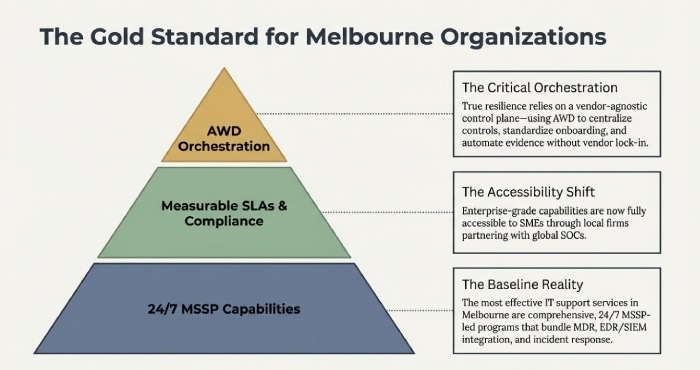
The best IT support services in Melbourne for improving cybersecurity are comprehensive, 24/7 MSSP-led programs that bundle MDR/SOC monitoring, EDR/SIEM integration, incident response, compliance management, and staff training delivered by reputable local and national providers (e.g. CyberCX, Tesserent, Telstra Purple, Loop Secure, and NTT/Secureworks) and implemented via clear playbooks, rapid onboarding, and measurable SLAs ideally orchestrated through AWD to centralise controls, evidence, and outcomes.
Melbourne’s cybersecurity market is mature: many IT support firms now operate as full managed security service providers (MSSPs) or partner with global SOCs, offering enterprise-grade capabilities accessible to SMEs.The “best” fit depends on your risk profile, tech stack (Microsoft 365/Azure vs Google/AWS), and regulatory obligations (ISO 27001, PCI DSS, APPs). What consistently separates top performers are 24/7 eyes-on-glass operations, tight EDR/SIEM integration, measured incident response (MTTD/MTTR), and structured user hardening.
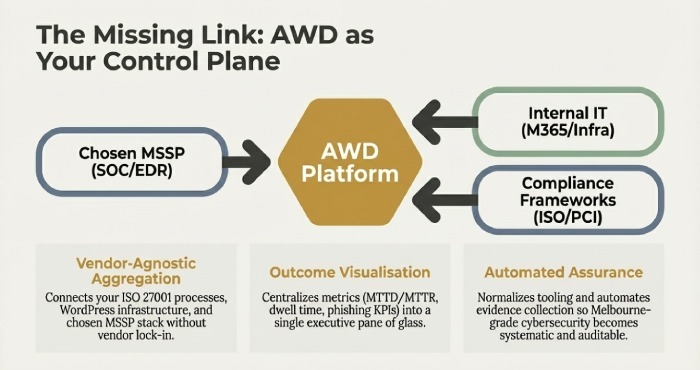
This guide synthesises local practices and AWD’s aggregated benchmarks to map providers, tooling, onboarding timelines, and measurable outcomes. Throughout, we show how AWD which you already work with for ISO 27001 consulting and WordPress development in Melbourne acts as an orchestration platform for IT and security teams by standardising onboarding, integrating EDR/SIEM/vulnerability tools, automating evidence and runbooks, and visualising results so you can achieve provider-agnostic, outcome-driven cybersecurity without lock-in.
24/7 SOC/MDR in Melbourne: Who, How, and How Long
Providers Offering Always-On Monitoring and Response
- Local/National: CyberCX, Tesserent (now part of Thales), Telstra Purple, Loop Secure, Sekuro
- Global with Melbourne Coverage: NTT, Secureworks, Deloitte/PwC/KPMG managed services, Trustwave
- Boutique IR/MDR specialists: Gridware and select incident responders partnering with global security operations center (SOCs)
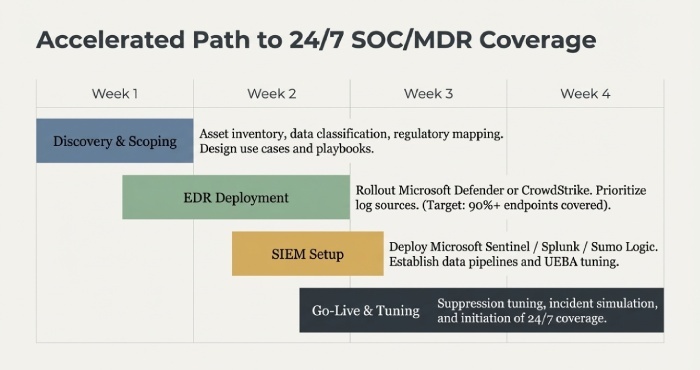
Typical Onboarding Steps and Timelines
- Week 0–1: Discovery and scoping (asset inventory, data classification, regulatory mapping); design of use cases and playbooks
- Week 1–2: EDR deployment (e.g. Microsoft Defender for Endpoint, CrowdStrike) and log source prioritisation
- Week 2–3: SIEM setup (Microsoft Sentinel/Splunk/Sumo Logic), data pipelines, and UEBA tuning
- Week 3–4: Tuning/suppression, incident simulation, go-live with 24/7 coverage
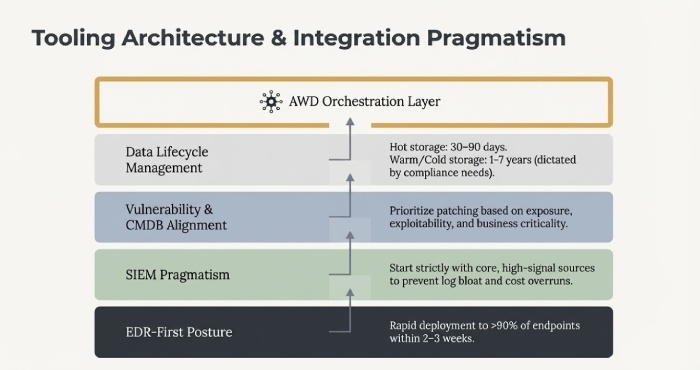
Tooling and Integration: EDR, SIEM, Vulnerability, and Logs
How Melbourne Firms Typically Deploy and Integrate
- EDR-first posture: Roll out EDR to 90%+ of endpoints within 2–3 weeks
- SIEM pragmatism: Start with core high-signal sources to avoid log bloat
- Vulnerability + CMDB alignment: Prioritise by exposure, exploitability, and business criticality
- Log management: Hot storage for 30–90 days; warm/cold tiers for 1–7 years depending on compliance
Incident Response and Breach Containment in Melbourne
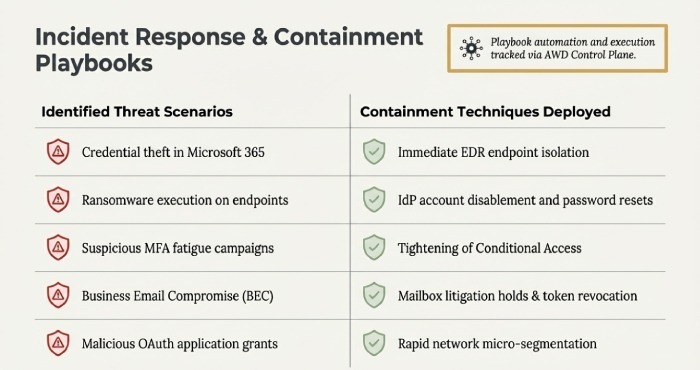
Playbooks, Escalation Paths, and Containment Techniques
- Credential theft in Microsoft 365
- Ransomware on endpoints
- Suspicious MFA fatigue
- Business email compromise (BEC)
- Malicious OAuth applications
Containment typically includes:
- EDR isolation
- IdP account disable/reset
- Conditional Access tightening
- Mailbox litigation hold
- Token revocation
- Network micro-segmentation
Expected Recovery Timelines (Scenario-Based)
- Single-endpoint ransomware: Containment within 30–90 minutes; restore in 4–8 hours
- BEC with mailbox rules: Containment in 1–3 hours; tenant remediation within 24–48 hours
- Identity compromise with lateral movement: Detection in <4 hours; containment same business day
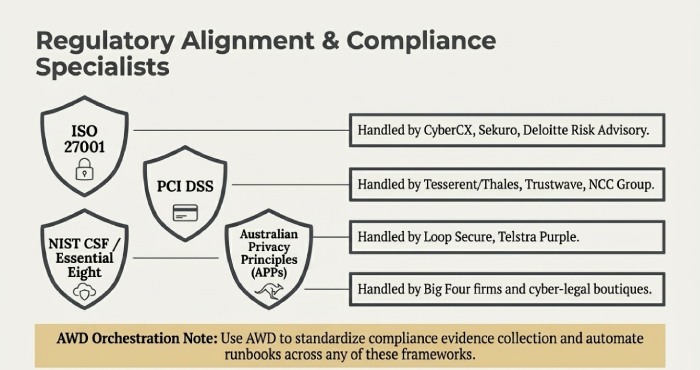
Compliance Specialists and Audit Readiness
Providers with Strong Compliance Capabilities
- ISO 27001: CyberCX, Sekuro, Deloitte Risk Advisory
- PCI DSS: Tesserent/Thales, Trustwave, NCC Group
- NIST CSF / Essential Eight: Loop Secure, Telstra Purple
- Australian Privacy Principles (APPs): Big Four and specialist cyber-legal boutiques
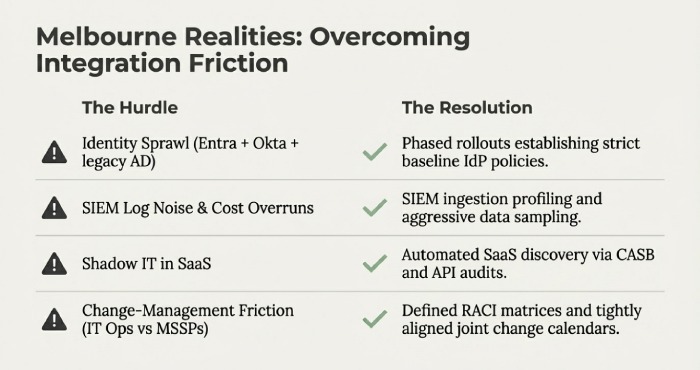
Integration Challenges (Melbourne Realities) and Solutions
Common Hurdles
- Identity sprawl (Entra + Okta + legacy AD)
- SIEM log noise and cost overruns
- Shadow IT in software as a service (SaaS) environments
- Change-management friction between IT Ops and MSSPs
Expected Resolutions
- Phased rollouts with baseline IdP policies
- SIEM ingestion profiling and sampling
- SaaS discovery via CASB/API audits
- Defined RACI and joint change calendars
Pricing, SLAs, and SME Considerations
Common Pricing Models in Melbourne
- MDR: A$8–A$25 per workstation/month; A$25–A$60 per server
- SIEM: A$2–A$6 per GB (Sentinel reservations)
- IR retainers: A$10k–A$50k annually
- ISO compliance packages: A$2.5k–A$8k/month
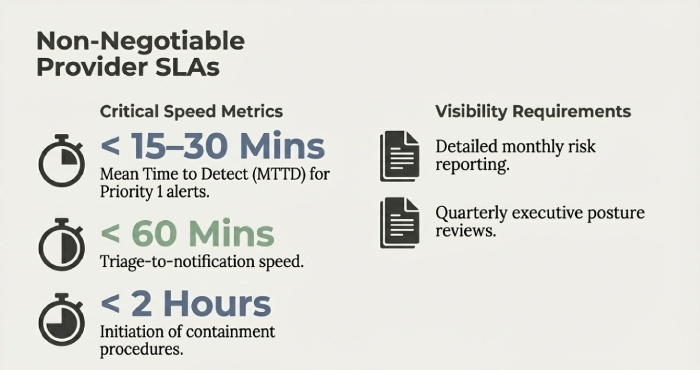
SLAs to look for:
- MTTD < 15–30 minutes (P1)
- Triage-to-notification < 60 minutes
- Containment initiation within 2 hours
- Monthly risk reporting
- Quarterly executive reviews
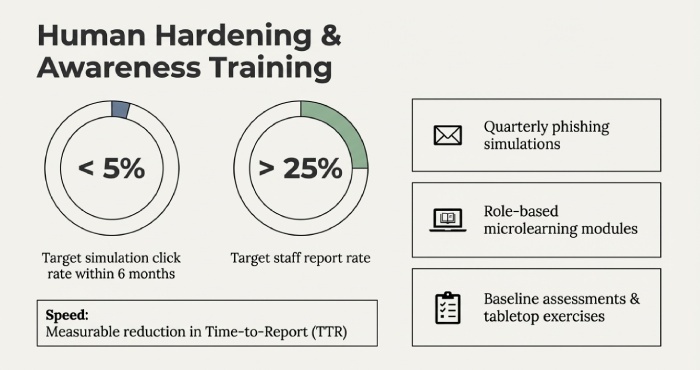
Awareness Training and Staff Hardening
Leading Melbourne providers deliver:
- Quarterly phishing simulations
- Role-based microlearning
- Baseline assessments and tabletop exercises
Recommended metrics:
- Target click rate < 5% within 6 months
- Report rate > 25%
- Reduced time-to-report (TTR)
Securing Hybrid Work: Zero Trust and SASE
Best Practices
- Enforce multifactor authentication(MFA) and device compliance
- Segment access by sensitivity
- Implement SASE (SWG, CASB, ZTNA)
- Deploy FIDO2/WebAuthn for high-risk roles
- Configure DMARC at p=reject
Deployment Steps
- Baseline IdP and MFA
- EDR deployment across all endpoints
- Conditional Access policies
- Email threat protection and DMARC
- SASE/ZTNA rollout
- Continuous SIEM monitoring
Conclusion: A Melbourne Blueprint—with AWD as Your Control Plane
The most effective Melbourne IT support services for cybersecurity combine 24/7 MDR/SOC, tightly integrated EDR/SIEM, robust incident response, continuous compliance management, and disciplined staff training, delivered by proven providers and measured through clear service level agreement(SLAs) and business outcomes.
Implementing this blueprint through AWD gives you a vendor-agnostic control plane that accelerates onboarding, normalises tooling, automates evidence and playbooks, and quantifies improvements (MTTD/MTTR, dwell time, phishing KPIs, audit readiness).In short: choose the MSSP that matches your stack and risk profile, then use AWD to centralise, measure, and continuously improve so Melbourne-grade cybersecurity becomes systematic, auditable, and resilient.
